(CVE-2025-50170) Windows Cloud Files Mini Filter Driver Elevation of Privilege
CVE: CVE-2025-50170
Affected Versions: Windows 10 (1809, 21H2, 22H2), Windows 11 (22H2, 23H2, 24H2), Windows Server 2019, 2022, 2025
CVSS3.1: 7.8 (High) — CVSS:3.1/AV:L/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H
Summary
| Product | Windows Cloud Files Mini Filter Driver (cldflt.sys) |
|---|---|
| Vendor | Microsoft |
| Severity | High — an unprivileged local attacker may corrupt arbitrary files to achieve code execution as SYSTEM |
| Affected Versions | Windows 10 (1809, 21H2, 22H2), Windows 11 (22H2, 23H2, 24H2), Windows Server 2019 / 2022 / 2025 |
| Tested Versions | Windows 11 23H2 (Build 22631.4249) |
| CVE Identifier | CVE-2025-50170 |
| CVE Description | A logic error in the Windows Cloud Files Mini Filter Driver allows an unprivileged local attacker to corrupt arbitrary files and execute code as SYSTEM |
| CWE Classification(s) | CWE-280: Improper Handling of Insufficient Permissions or Privileges |
CVSS3.1 Scoring System
Base Score: 7.8 (High)
Vector String: CVSS:3.1/AV:L/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H
| Metric | Value |
|---|---|
| Attack Vector (AV) | Local |
| Attack Complexity (AC) | Low |
| Privileges Required (PR) | Low |
| User Interaction (UI) | None |
| Scope (S) | Unchanged |
| Confidentiality (C) | High |
| Integrity (I) | High |
| Availability (A) | High |
Product Background
cldflt.sys is a filesystem minifilter driver that acts as a proxy between user applications and cloud sync engines. The sync engine handles on-demand downloading and uploading of data, while cldflt.sys works with the Windows Shell to present cloud-backed files as if they were locally available. It underpins technologies such as OneDrive.
Description of the vulnerability
A logic error during creation of placeholder files allows an unprivileged attacker to corrupt arbitrary files on the system, which can be leveraged to execute arbitrary code as SYSTEM.
Users of cldflt can create placeholder files under syncroot directories via the cldapi.dll!CfCreatePlaceholders() usermode API, which internally calls cldflt.sys!HsmpOpCreatePlaceholders() in the kernel.
This function accepts a usermode pointer, creates an MDL from it, and maps it to system memory:
MemoryDescriptorList = IoAllocateMdl(UserPtr, UserPtrLen, 0, 0, 0LL);
ProbeForRead(UserPtr, UserPtrLen, 4u);
v10 = MemoryDescriptorList;
MmProbeAndLockPages(MemoryDescriptorList, 1, IoReadAccess);
if ( (MemoryDescriptorList->MdlFlags & 5) != 0 )
MappedSystemVa = MemoryDescriptorList->MappedSystemVa;
else
MappedSystemVa = MmMapLockedPagesSpecifyCache(MemoryDescriptorList, 0, MmCached, 0LL, 0, 0x40000010u);
The developer specified IoReadAccess when probing the usermode pointer, signalling the address is only used to read data. However, the function subsequently writes to this address in multiple places.
It writes FILE_BASIC_INFORMATION data directly at address + 0x10:
status_ = FltQueryInformationFile(Instance, FileObject, &v72, 0x28u, FileBasicInformation, 0LL);
HsmDbgBreakOnStatus(status_);
if ( status_ >= 0 )
{
*(curEntry_ + 0x10) = v72; // curEntry_ points to the user-supplied address
goto LABEL_158;
}
And it writes an error status at address + 0x40:
*(curEntry_ + 0x40) = status_;
Because the kernel writes to this address without verifying write access, an attacker can map a read-only file to that address and pass it to the kernel, causing the file to be overwritten.
The attacker can further bypass internal validations and precisely control the write offset by spraying a writable page contiguous in virtual memory with the read-only target file:
puts("first create neighbouring page");
for (DWORD counter = 1; ; counter++) {
attackerView = MapViewOfFile(hAttackerMap, FILE_MAP_ALL_ACCESS, 0, 0, 0);
victimView = MapViewOfFile(hVictimMap, FILE_MAP_READ, 0, 0, 0);
if (attackerView + 0x10000 == victimView)
break;
printf("trying %d\n", counter);
}
By mapping a 0x10000-byte attacker-controlled region immediately before the victim read-only file, the attacker passes victimView - 0x40 as the usermode pointer. The first 0x40 bytes fall within the attacker-controlled writable region and pass all internal validations (only the first 0x10 bytes are checked), while the kernel write lands precisely at the start of the victim file.
Impact
File corruption: Corrupting core system binaries or data storage. For example, corrupting a shell script executed as SYSTEM — such as one containing cmd.exe /c C:\Windows\System32\notepad.exe — to redirect execution to an attacker-controlled directory achieves arbitrary code execution. Normal users can create directories under C:\, making this escalation practical.
In-memory corruption: Because all copies of a loaded DLL across different processes share the same physical memory pages, this bug can corrupt DLLs and EXEs that are currently loaded and running — without leaving any traces on disk. This can be abused to kill security processes or introduce subtle, forensically invisible backdoors.
Proof of Concept
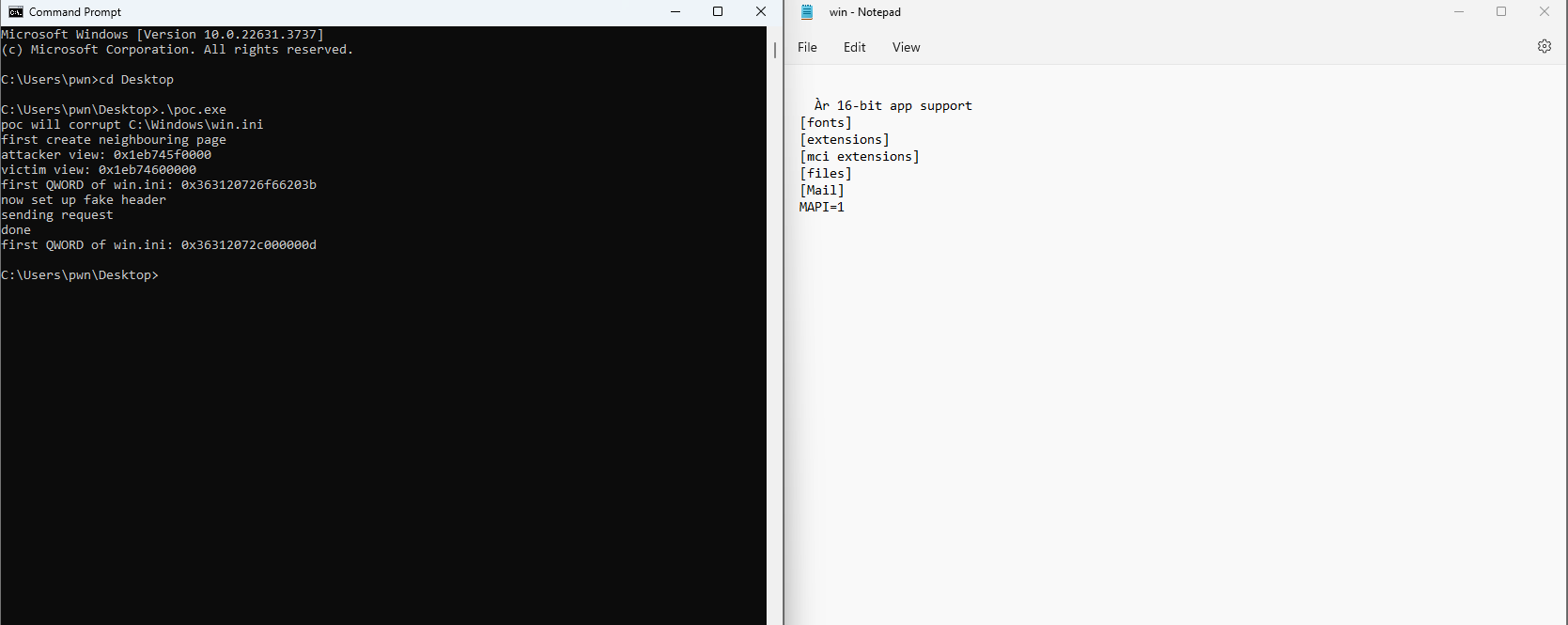
The PoC corrupts C:\Windows\win.ini to demonstrate arbitrary file write. Below, the left pane shows the PoC output confirming the first QWORD of win.ini changed from 0x363120726f66203b to 0x36312072c000000d. The right pane shows the resulting corrupted file opened in Notepad.
Credit
Chen Le Qi of STAR Labs SG Pte. Ltd.
Timeline
- 2025-08-12 — Patch released via Microsoft Security Response Center (August 2025 Patch Tuesday)
