Summer Pwnables: When the Heat Rises, So Do the C-Shells 🔥
Table of Contents
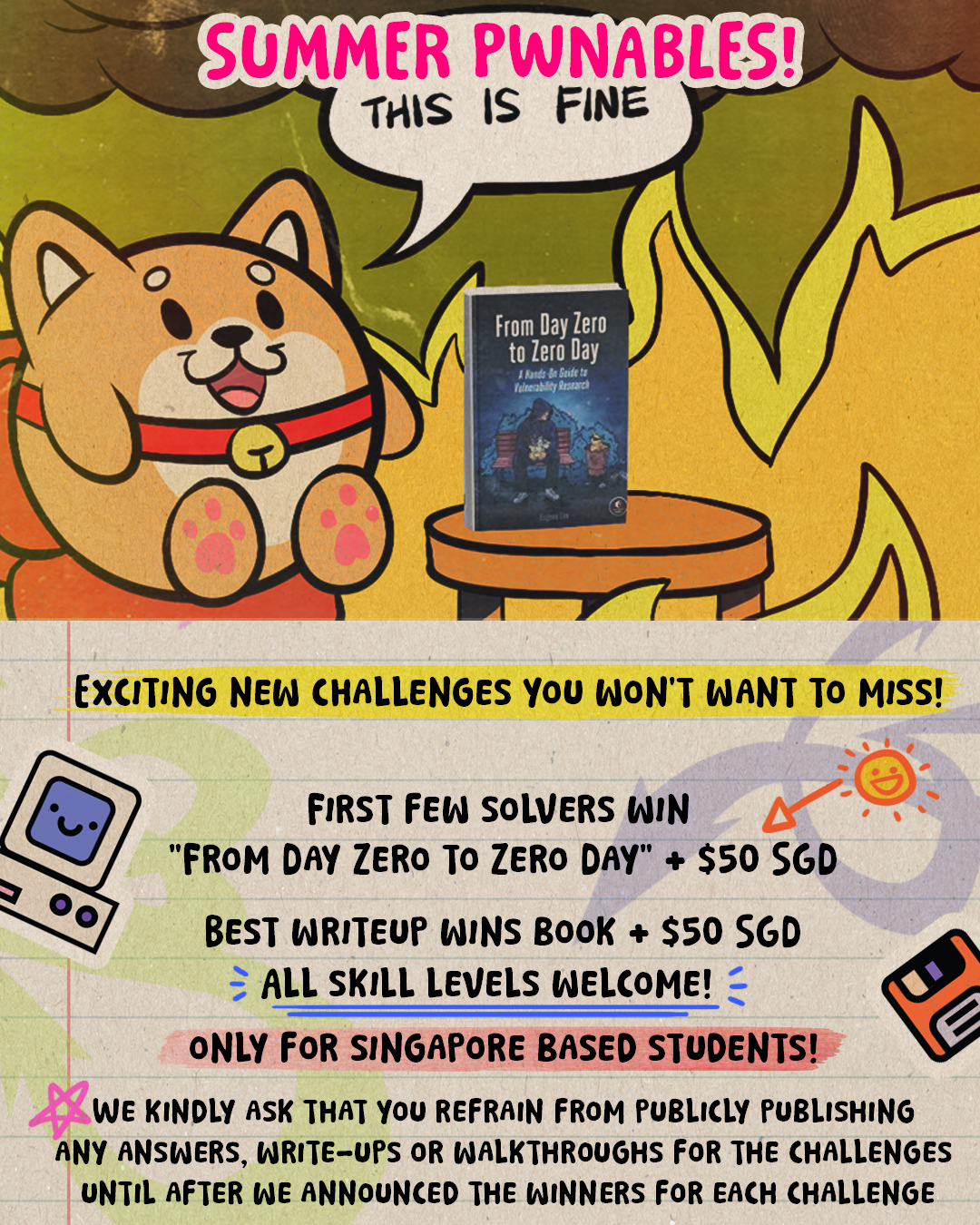
🌴☀️ SUMMER PWNABLES 2025 ☀️🌴
The hottest hacking challenge on this side of Southeast Asia!
Think you can handle the heat? Time to prove your l33t skills are more than just talk! 😎🔥
The summer sun isn’t the only thing burning bright – we have cooked up some seriously spicy challenges that will test whether you are a true shell wizard! 🧙♂️✨
📍 ELIGIBILITY REQUIREMENTS
This challenge is exclusively open to Singapore-based students only!
You must be currently enrolled in a Singapore educational institution to participate.
🎯 THE FIRST MISSION (Should You Choose to Accept It)
Your objective, should you dare to accept: Transform from zero to hero by achieving the ultimate prize – Gain Code Execution Access! But here’s the catch: Imagine you’ve found a bug in the linux gzip tool… One that can potentially trigger a reverse shell if a malicious payload is passed Your job is to craft that payload… be very subtle 🥷 One wrong move and… 💀
🏆 THE ARENA RULES
(Read carefully, or face the wrath of the admins!)
🔴 Rule #1: Get Code Execution or go home! Exploit the challenges like a true pwn master
🔴 Rule #2: Submit your exploit source code + epic writeup to this form here – we want to see your thought process!
🔴 Rule #3: Think you’ve spotted the vuln but running out of time? Send us your theoretical exploitation writeup anyway – partial credit for big brains! 🧠
🎁 LEGENDARY LOOT AWAITS!
For the Speed Demons: 🥇
First few hackers to achieve code execution will claim the legendary “From Day Zero to Zero Day” book by Eugene “Spaceraccoon” Lim – complete with author’s signature! + $50 $100 SGD cash prize 💵
For the Wordsmith Warriors: 🏆
Best writeup wins the same epic tome + $50 $100 SGD cash prize 💵! Show us your technical storytelling skills – make us feel like we’re right there in the terminal with you!
Prize Collection: Winners must collect their rewards in person on 29th August 2025 📅 We will contact you.
Download the challenges: CHALLENGE #001 ⬇️
(Warning: May cause excessive coffee consumption and late-night coding sessions)
The password to the zip file is “baby_blastpass”
Once you have a working exploit, send your payload to 159.223.33.156 9101 and get the flag!
File Integrity Check:
📋 sha256 of lz1.zip: 5b0c41b916530b16a2a7d87eff4fb426357fefba0e8c0cf41c06bd6725c2b8fc
Original lz1 code by andyherbert: https://github.com/andyherbert/lz1
“Every system has a weakness. Every wall has a crack. Every challenge… has a solution.”
Your time is NOW!
Credits:
-
Challenge Creators: Muhammad Alifa Ramdhan & Zafir Rasyidi Taufik
-
Challenge Testers: Nguyen Dang Nguyen, Chen Le Qi
-
Poster Designer: Sarah Tan
